Gcov is used to analyze code coverage – which lines of code have actually been executed while running an application. Lcov is a tool that can produce HTML reports from the gcov output. If you have a suite of unit tests that you run on your code, you can use these tools to see which the lines of code are covered by your tests and which are not. I can't be sure which change finally did the trick for me but I think it was the -fprofile-generate flag. Using GNAT GPS I went to the Switches tab on the left and then selected the Ada Linker tab on the top. Then I enabled the checkbox for Code Coverage.Oh yeah I've found that on the Builder tab in that same area if you enable the Recompile if switches changed checkbox it can save a lot of.
From Mac OS X 10.9 onward, if Xcode is already installed in Mac OS X then Command Line Tools becomes installed as well (you can check this by trying to run gcc or make from the terminal). Accordingly, this tutorial is aimed at users who do not want to install the broader Xcode development package, and would rather only have the command line. However, I found the way to get this to work. I have presented the steps that work with the sample project below. The steps work for Linux/Mac. Similar steps would work even on Windows once you have installed lcov. On Mac, you can install lcov using Mac Ports. Go to the Debug folder of the sample project. gcovvarported.filename contains the full path of the.gcda file to create. On Mac, install lcov using mac ports. On Linux, it should be there or find your Linux flavor specific package. Go to your build directory where your object files,.gcno files and.gcda files are there.
This article has been migrated from my original post at embeddedinn.wordpress.com.
Any large code base needs to be incrementally tested for each release for regressions and bugs. When the code base grows, manual testing fails to meet the requirements and we have to move into automated systems for testing. Once a test is written, we have excellent continuous integration systems like Jenkins or Cruise Control to validate the tests against any changes made on the code. However, the CI system is only as effective as the test. If the test does not cover all use cases, then there is no point in running the tests in CI.
This article intends to illustrate the use of ‘gcov' to estimate the dynamic coverage of a test. The article speaks solely from the viewpoint of a C programmer working on a Linux PC (or similar systems)
What is coverage?
All large scale, usable C code is written in the form of blocks of code enclosed in functions. A block can be a set of simple execution statements or a logical branch.
The ideal test code should logically call all the functions and execute all statements in the blocks. The percentage of lines of actual code that gets executed when a test code runs is called the coverage of the test code. More the number of lines of code that is tested, less is the probability to get a last minute surprise bug.
There are two types of coverage analysis that is possible.
Static code coverage analysis is done by analyzing the test code and the actual code to primarily estimate the function call coverage. Static code coverage analysis is much faster and simpler since the generated object file need not be executed. This is particularly handy in the case of small scale embedded systems.
Dynamic code coverage analysis is much more elaborate and requires the test code to be executed on the target. It also requires the object file to be generated with special compilation options. However, it gives much more detailed analysis of how effective the test is.
For obvious reasons, it is not practical to manually compute the coverage of a test code. Thus we have some tools that can compute the coverage of our test code for us. We will now look into the details of how ‘gcov' can be used for dynamic code coverage analysis.
GCOV
Gcov Macos
As per Wikipedia, Gcov is a source code coverage analysis and statement-by-statement profiling tool. Gcov generates exact counts of the number of times each statement in a program is executed and annotates source code to add instrumentation. Gcov comes as a standard utility with GNU CC Suite (GCC)
Gcov provides the following details:
- How often each line of code executes
- What lines of code are actually executed
- How much computing time each section of code uses
Getting Started With GCOV
When using gcov, you must first compile your program with –coverage GCC option.
This tells the compiler to generate additional information needed by gcov (basically a flow graph of the program) and also includes additional code in the object files for generating the extra profiling information needed by gcov. These additional files (.gcno) are placed in the directory where the object file is located.
Once the object file is generated, execute it once to get the profile file (.gcda)
Once we have the gcna and gcda files , we can now run gcov.
To illustrate the usage of gcov, we will consider a very minimal library (lib.c) and it test suite (test.c) .
lib.c
test.c
Compilation command for the test code :
gcc --coverage lib.c test.c –o test
This will generate the following files:
lib.gcno– library flow graphtest.gcno– test code flow graphtest– test code executable
Now, execute the test code object file. This will generate the following files
lib.gcda– library profile outputtest.gcda– test code profile output
Now we have all the inputs required for gcov to generate the coverage report. To generate the coverage report, run the following command
gcov -abcfu lib.c
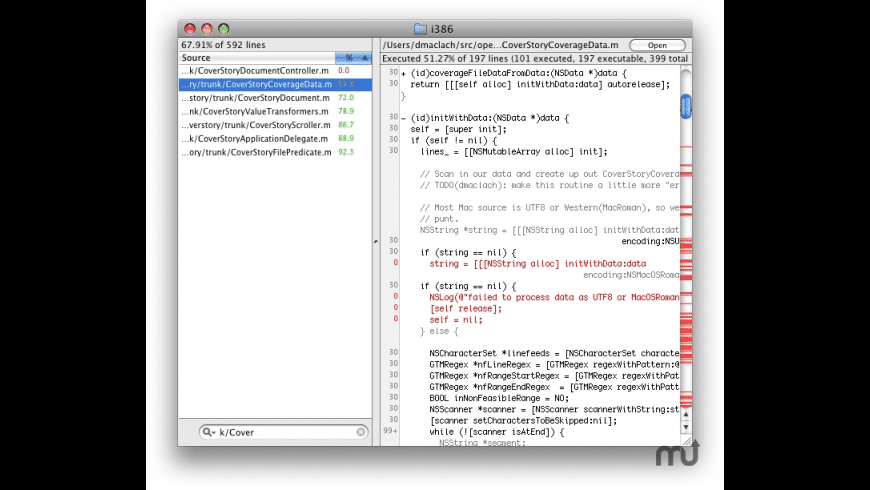
Coverage summary will be displayed as below when gcov finishes execution:
Detailed coverage report will be available in the lib.c.gcov file generated by gcov
Each block is marked by a line with the same line number as the last line of the block and the number of branch and calls in the block.
Each function is preceded with a line showing the number of times the function is called, number of times it returns and the percentage of function blocks that were executed.
Each line of executable code contains the number of times the line was executed and the actual source code line number. Any line that was not executed will have ##### in place of the execution count. Blocks that are not executed will have $$$$$ in place of the execution count.
The command line option summary for gcov is given below:
| -h, –help | Print this help, then exit |
| -v, –version | Print version number, then exit |
| -a, –all-blocks | Show information for every basic block |
| -b, –branch-probabilities | Include branch probabilities in output |
| -c, –branch-counts | Given counts of branches taken rather than percentages |
| -n, –no-output | Do not create an output file |
| -l, –long-file-names | Use long output file names for included source files |
| -f, –function-summaries | Output summaries for each function |
| -o, –object-directory | DIRFILE Search for object files in DIR or called FILE |
| -p, –preserve-paths | Preserve all pathname components |
| -u, –unconditional-branches | Show unconditional branch counts |
Visualizing results with LCOV
The Linux testing project (LTP) has come up with a tool called lcov that provides a more user-friendly graphical visualization of the gcov output. It generates html files and integrates well with web based CI systems.
To make lcov generate html reports for you, give the following commands once the gcno and gcda files are generated.
lcov --directory . –zerocounterslcov --directory . --capture --output-file app.infogenhtml app.info
The lcov reports seen from a browser is shown in the screenshots below.
Cross Profiling
This section is adapted from the GCOV manual :
As we have seen so far, running the program to be profiled will cause profile output to be generated. For each source file compiled with the –coverage option, a .gcda file will be generated in the object file directory. This places a restriction that the target system should have the same directory structure. (The program will try to create the needed directory structure, if it is not already present).
As per the gnu GCOV documentation, redirection can be done with the help of two execution environment variables.
GCOV_PREFIX: Contains the prefix to add to the absolute paths in the object file. Prefix can be absolute, or relative. The default is no prefix.GCOV_PREFIX_STRIP: Indicates the how many initial directory names to strip off the hardwired absolute paths. Default value is0.
Note: If GCOV_PREFIX_STRIP is set without GCOV_PREFIX is undefined, then a relative path is made out of the hardwired absolute paths.
For example, if the object file /user/build/foo.o was built with -fprofile-arcs, the final executable will try to create the data file /user/build/foo.gcda when running on the target system. This will fail if the corresponding directory does not exist and it is unable to create it. This can be overcome by, for example, setting the environment as GCOV_PREFIX=/target/run and GCOV_PREFIX_STRIP=1. Such a setting will name the data file /target/run/build/foo.gcda.
You must move the data files to the expected directory tree in order to use them for profile directed optimizations (–use-profile), or to use the gcov tool.
NOTE:
Between mid October 2019 and mid February 2020 everyone in the Army was migrated to use their PIV Authentication certificate for Email access. You no longer use the Email certificate for Enterprise Email or any CAC enabled websites
Mac users who choose to upgrade (or already have upgraded) to Mac OS Catalina (10.15.x) will need to uninstall all 3rd Party CAC enablers per https://militarycac.com/macuninstall.htm AND reenable the built in smart card ability (very bottom of macuninstall link above)
If you purchased your Mac with OS Catalina (10.15.x) already installed, you can skip the uninstall part above and follow the instructions below.
6 'high level' steps needed, follow down the page to make this a painless systematic process
| 1. | Is your CAC reader 'Mac friendly'? |
| 2. | Can your Mac 'see' the reader? |
| 3. | Verify which version of Mac OS you have |
| 4. | Figure out which CAC (ID card) you have |
| 5. | Install the DoD certificates |
| 5a. | Additional DoD certificate installation instructions for Firefox users |
| 6. | Decide which CAC enabler you want to use (except for 10.12-.15 & 11) |
Install Lcov Mac
Step 1: Is your CAC reader Mac friendly?
Visit the USB Readers page to verify the CAC reader you have is Mac friendly.
Visit the USB-C Readers page to verify the CAC reader you have is Mac friendly.
'Some, not all' CAC readers may need to have a driver installed to make it work.
NOTE: Readers such as: SCR-331 & SCR-3500A may need a firmware update (NO OTHER Readers need firmware updates).
Information about these specific readers are in Step 2
Step 2: Can your Mac 'see' the reader?
Plug the CAC reader into an open USB port before proceeding, give it a few moments to install
Step 2a: Click the Apple Icon in the upper left corner of the desktop, select 'About This Mac'
Step 2b: Click 'System Report..' (button)
Step 2c: Verify the CAC reader shows in Hardware, USB, under USB Device Tree. Different readers will show differently, most readers have no problem in this step. See Step 2c1 for specific reader issues.
Step 2c1: Verify firmware version on your SCR-331 or GSR-202, 202V, 203 CAC, or SCR-3500a reader. If you have a reader other than these 5, Proceed directly to step 3
Step 2c1a-SCR-331 reader
If your reader does not look like this, go to the next step.
In the 'Hardware' drop down, click 'USB.' On the right side of the screen under 'USB Device Tree' the window will display all hardware plugged into the USB ports on your Mac. Look for 'SCRx31 USB Smart Card Reader.' If the Smart Card reader is present, look at 'Version' in the lower right corner of this box: If you have a number below 5.25, you need to update your firmware to 5.25. If you are already at 5.25, your reader is installed on your system, and no further hardware changes are required. You can now Quit System Profiler and continue to Step 3.
Step 2c1b-SCR-3500A reader
If you have the SCR3500A P/N:905430-1 CAC reader,you may need to install this driver, as the one that installs automatically will not work on most Macs. Hold the control key [on your keyboard] when clicking the .pkg file [with your mouse], select [the word] Open
Step 3: Verify which version of MacOS do you have?
(You need to know this information for step 6)
Step 3a: Click the Apple Icon in the upper left corner of your desktop and select 'About This Mac'
Step 3b: Look below Mac OS X for: Example: Version 10.X.X.
Step 4: Figure out which CAC (ID Card) you have
(You need to know this information for step 6)
Look at the top back of your ID card for these card types. If you have any version other than the six shown below, you need to visit an ID card office and have it replaced. All CACs [other than these six] were supposed to be replaced prior to 1 October 2012.
Find out how to flip card over video
Step 5: Install the DoD certificates (for Safari and Chrome Users)
Go to Keychain Access
Click: Go (top of screen), Utilities, double click Keychain Access.app
(You can also type: keychain access using Spotlight (this is my preferred method))
Select login (under Keychains),and All Items (under Category).
Download the 5 files via links below (you may need to click, select Download Linked File As.. on each link) Save to your downloads folder
Please know.. IF You have any DoD certificates already located in your keychain access, you will need to delete them prior to running the AllCerts.p7b file below.
https://militarycac.com/maccerts/AllCerts.p7b,
https://militarycac.com/maccerts/RootCert2.cer,
https://militarycac.com/maccerts/RootCert3.cer,
https://militarycac.com/maccerts/RootCert4.cer, and
Double click each of the files to install certificates into the login section of keychain
Select the Kind column, verify the arrow is pointing up, scroll down to certificate, look for all of the following certificates:
DOD EMAIL CA-33 through DOD EMAIL CA-34,
DOD EMAIL CA-39 through DOD EMAIL CA-44,
DOD EMAIL CA-49 through DOD EMAIL CA-52,
Gov For Michigan Vote Primary
DOD EMAIL CA-59,
DOD ID CA-33 through DOD ID CA-34,
DOD ID CA-39 through DOD ID CA-44,
DOD ID CA-49 through DOD ID CA-52,
DOD ID CA-59
DOD ID SW CA-35 through DOD ID SW CA-38,
DOD ID SW CA-45 through DOD ID SW CA-48,
DoD Root CA 2 through DoD Root CA 5,
DOD SW CA-53 through DOD SW CA-58, and
DOD SW CA-60 through DOD SW CA-61
NOTE: If you are missing any of the above certificates, you have 2 choices,
1. Delete all of them, and re-run the 5 files above, or
2. Download the allcerts.zip file and install each of the certificates you are missing individually.
Errors:
Error 100001 Solution
Error 100013 Solution
Gcov For Macbook
You may notice some of the certificates will have a red circle with a white X . This means your computer does not trust those certificates
You need to manually trust the DoD Root CA 2, 3, 4, & 5 certificates
Double click each of the DoD Root CA certificates, select the triangle next to Trust, in the When using this certificate: select Always Trust, repeat until all 4 do not have the red circle with a white X.
You may be prompted to enter computer password when you close the window
Once you select Always Trust, your icon will have a light blue circle with a white + on it.
The 'bad certs' that have caused problems for Windows users may show up in the keychain access section on some Macs. These need to be deleted / moved to trash.
The DoD Root CA 2 & 3 you are removing has a light blue frame, leave the yellow frame version. The icons may or may not have a red circle with the white x
| or | DoD Interoperability Root CA 1 or CA 2 | certificate | |
| DoD Root CA 2 or 3 (light blue frame ONLY) | certificate | ||
| or | Federal Bridge CA 2016 or 2013 | certificate | |
| or | Federal Common Policy CA | certificate | |
| or | or | SHA-1 Federal Root CA G2 | certificate |
| or | US DoD CCEB Interoperability Root CA 1 | certificate |
If you have tried accessing CAC enabled sites prior to following these instructions, please go through this page before proceeding Fast gsm unlock free download.
Clearing the keychain (opens a new page)
Please come back to this page to continue installation instructions.
Step 5a: DoD certificate installation instructions for Firefox users
NOTE: Firefox will not work on Catalina (10.15.x), or last 4 versions of Mac OS if using the native Apple smartcard ability
Download AllCerts.zip, [remember where you save it].
double click the allcerts.zip file (it'll automatically extract into a new folder)
Option 1 to install the certificates (semi automated):
From inside the AllCerts extracted folder, select all of the certificates
Coverage summary will be displayed as below when gcov finishes execution:
Detailed coverage report will be available in the lib.c.gcov file generated by gcov
Each block is marked by a line with the same line number as the last line of the block and the number of branch and calls in the block.
Each function is preceded with a line showing the number of times the function is called, number of times it returns and the percentage of function blocks that were executed.
Each line of executable code contains the number of times the line was executed and the actual source code line number. Any line that was not executed will have ##### in place of the execution count. Blocks that are not executed will have $$$$$ in place of the execution count.
The command line option summary for gcov is given below:
| -h, –help | Print this help, then exit |
| -v, –version | Print version number, then exit |
| -a, –all-blocks | Show information for every basic block |
| -b, –branch-probabilities | Include branch probabilities in output |
| -c, –branch-counts | Given counts of branches taken rather than percentages |
| -n, –no-output | Do not create an output file |
| -l, –long-file-names | Use long output file names for included source files |
| -f, –function-summaries | Output summaries for each function |
| -o, –object-directory | DIRFILE Search for object files in DIR or called FILE |
| -p, –preserve-paths | Preserve all pathname components |
| -u, –unconditional-branches | Show unconditional branch counts |
Visualizing results with LCOV
The Linux testing project (LTP) has come up with a tool called lcov that provides a more user-friendly graphical visualization of the gcov output. It generates html files and integrates well with web based CI systems.
To make lcov generate html reports for you, give the following commands once the gcno and gcda files are generated.
lcov --directory . –zerocounterslcov --directory . --capture --output-file app.infogenhtml app.info
The lcov reports seen from a browser is shown in the screenshots below.
Cross Profiling
This section is adapted from the GCOV manual :
As we have seen so far, running the program to be profiled will cause profile output to be generated. For each source file compiled with the –coverage option, a .gcda file will be generated in the object file directory. This places a restriction that the target system should have the same directory structure. (The program will try to create the needed directory structure, if it is not already present).
As per the gnu GCOV documentation, redirection can be done with the help of two execution environment variables.
GCOV_PREFIX: Contains the prefix to add to the absolute paths in the object file. Prefix can be absolute, or relative. The default is no prefix.GCOV_PREFIX_STRIP: Indicates the how many initial directory names to strip off the hardwired absolute paths. Default value is0.
Note: If GCOV_PREFIX_STRIP is set without GCOV_PREFIX is undefined, then a relative path is made out of the hardwired absolute paths.
For example, if the object file /user/build/foo.o was built with -fprofile-arcs, the final executable will try to create the data file /user/build/foo.gcda when running on the target system. This will fail if the corresponding directory does not exist and it is unable to create it. This can be overcome by, for example, setting the environment as GCOV_PREFIX=/target/run and GCOV_PREFIX_STRIP=1. Such a setting will name the data file /target/run/build/foo.gcda.
You must move the data files to the expected directory tree in order to use them for profile directed optimizations (–use-profile), or to use the gcov tool.
NOTE:
Between mid October 2019 and mid February 2020 everyone in the Army was migrated to use their PIV Authentication certificate for Email access. You no longer use the Email certificate for Enterprise Email or any CAC enabled websites
Mac users who choose to upgrade (or already have upgraded) to Mac OS Catalina (10.15.x) will need to uninstall all 3rd Party CAC enablers per https://militarycac.com/macuninstall.htm AND reenable the built in smart card ability (very bottom of macuninstall link above)
If you purchased your Mac with OS Catalina (10.15.x) already installed, you can skip the uninstall part above and follow the instructions below.
6 'high level' steps needed, follow down the page to make this a painless systematic process
| 1. | Is your CAC reader 'Mac friendly'? |
| 2. | Can your Mac 'see' the reader? |
| 3. | Verify which version of Mac OS you have |
| 4. | Figure out which CAC (ID card) you have |
| 5. | Install the DoD certificates |
| 5a. | Additional DoD certificate installation instructions for Firefox users |
| 6. | Decide which CAC enabler you want to use (except for 10.12-.15 & 11) |
Install Lcov Mac
Step 1: Is your CAC reader Mac friendly?
Visit the USB Readers page to verify the CAC reader you have is Mac friendly.
Visit the USB-C Readers page to verify the CAC reader you have is Mac friendly.
'Some, not all' CAC readers may need to have a driver installed to make it work.
NOTE: Readers such as: SCR-331 & SCR-3500A may need a firmware update (NO OTHER Readers need firmware updates).
Information about these specific readers are in Step 2
Step 2: Can your Mac 'see' the reader?
Plug the CAC reader into an open USB port before proceeding, give it a few moments to install
Step 2a: Click the Apple Icon in the upper left corner of the desktop, select 'About This Mac'
Step 2b: Click 'System Report..' (button)
Step 2c: Verify the CAC reader shows in Hardware, USB, under USB Device Tree. Different readers will show differently, most readers have no problem in this step. See Step 2c1 for specific reader issues.
Step 2c1: Verify firmware version on your SCR-331 or GSR-202, 202V, 203 CAC, or SCR-3500a reader. If you have a reader other than these 5, Proceed directly to step 3
Step 2c1a-SCR-331 reader
If your reader does not look like this, go to the next step.
In the 'Hardware' drop down, click 'USB.' On the right side of the screen under 'USB Device Tree' the window will display all hardware plugged into the USB ports on your Mac. Look for 'SCRx31 USB Smart Card Reader.' If the Smart Card reader is present, look at 'Version' in the lower right corner of this box: If you have a number below 5.25, you need to update your firmware to 5.25. If you are already at 5.25, your reader is installed on your system, and no further hardware changes are required. You can now Quit System Profiler and continue to Step 3.
Step 2c1b-SCR-3500A reader
If you have the SCR3500A P/N:905430-1 CAC reader,you may need to install this driver, as the one that installs automatically will not work on most Macs. Hold the control key [on your keyboard] when clicking the .pkg file [with your mouse], select [the word] Open
Step 3: Verify which version of MacOS do you have?
(You need to know this information for step 6)
Step 3a: Click the Apple Icon in the upper left corner of your desktop and select 'About This Mac'
Step 3b: Look below Mac OS X for: Example: Version 10.X.X.
Step 4: Figure out which CAC (ID Card) you have
(You need to know this information for step 6)
Look at the top back of your ID card for these card types. If you have any version other than the six shown below, you need to visit an ID card office and have it replaced. All CACs [other than these six] were supposed to be replaced prior to 1 October 2012.
Find out how to flip card over video
Step 5: Install the DoD certificates (for Safari and Chrome Users)
Go to Keychain Access
Click: Go (top of screen), Utilities, double click Keychain Access.app
(You can also type: keychain access using Spotlight (this is my preferred method))
Select login (under Keychains),and All Items (under Category).
Download the 5 files via links below (you may need to click, select Download Linked File As.. on each link) Save to your downloads folder
Please know.. IF You have any DoD certificates already located in your keychain access, you will need to delete them prior to running the AllCerts.p7b file below.
https://militarycac.com/maccerts/AllCerts.p7b,
https://militarycac.com/maccerts/RootCert2.cer,
https://militarycac.com/maccerts/RootCert3.cer,
https://militarycac.com/maccerts/RootCert4.cer, and
Double click each of the files to install certificates into the login section of keychain
Select the Kind column, verify the arrow is pointing up, scroll down to certificate, look for all of the following certificates:
DOD EMAIL CA-33 through DOD EMAIL CA-34,
DOD EMAIL CA-39 through DOD EMAIL CA-44,
DOD EMAIL CA-49 through DOD EMAIL CA-52,
Gov For Michigan Vote Primary
DOD EMAIL CA-59,
DOD ID CA-33 through DOD ID CA-34,
DOD ID CA-39 through DOD ID CA-44,
DOD ID CA-49 through DOD ID CA-52,
DOD ID CA-59
DOD ID SW CA-35 through DOD ID SW CA-38,
DOD ID SW CA-45 through DOD ID SW CA-48,
DoD Root CA 2 through DoD Root CA 5,
DOD SW CA-53 through DOD SW CA-58, and
DOD SW CA-60 through DOD SW CA-61
NOTE: If you are missing any of the above certificates, you have 2 choices,
1. Delete all of them, and re-run the 5 files above, or
2. Download the allcerts.zip file and install each of the certificates you are missing individually.
Errors:
Error 100001 Solution
Error 100013 Solution
Gcov For Macbook
You may notice some of the certificates will have a red circle with a white X . This means your computer does not trust those certificates
You need to manually trust the DoD Root CA 2, 3, 4, & 5 certificates
Double click each of the DoD Root CA certificates, select the triangle next to Trust, in the When using this certificate: select Always Trust, repeat until all 4 do not have the red circle with a white X.
You may be prompted to enter computer password when you close the window
Once you select Always Trust, your icon will have a light blue circle with a white + on it.
The 'bad certs' that have caused problems for Windows users may show up in the keychain access section on some Macs. These need to be deleted / moved to trash.
The DoD Root CA 2 & 3 you are removing has a light blue frame, leave the yellow frame version. The icons may or may not have a red circle with the white x
| or | DoD Interoperability Root CA 1 or CA 2 | certificate | |
| DoD Root CA 2 or 3 (light blue frame ONLY) | certificate | ||
| or | Federal Bridge CA 2016 or 2013 | certificate | |
| or | Federal Common Policy CA | certificate | |
| or | or | SHA-1 Federal Root CA G2 | certificate |
| or | US DoD CCEB Interoperability Root CA 1 | certificate |
If you have tried accessing CAC enabled sites prior to following these instructions, please go through this page before proceeding Fast gsm unlock free download.
Clearing the keychain (opens a new page)
Please come back to this page to continue installation instructions.
Step 5a: DoD certificate installation instructions for Firefox users
NOTE: Firefox will not work on Catalina (10.15.x), or last 4 versions of Mac OS if using the native Apple smartcard ability
Download AllCerts.zip, [remember where you save it].
double click the allcerts.zip file (it'll automatically extract into a new folder)
Option 1 to install the certificates (semi automated):
From inside the AllCerts extracted folder, select all of the certificates
click (or Right click) the selected certificates, select Open With, Other..
In the Enable (selection box), change to All Applications
Select Firefox, then Open
You will see several dozen browser tabs open up, let it open as many as it wants.
You will eventually start seeing either of the 2 messages shown next
If the certificate is not already in Firefox, a window will pop up stating 'You have been asked to trust a new Certificate Authority (CA).'
Check all three boxes to allow the certificate to: identify websites, identify email users, and identify software developers
or
'Alert This certificate is already installed as a certificate authority.' Click OK
Once you've added all of the certificates..
• Click Firefox (word) (upper left of your screen)
• Preferences
• Advanced (tab)
• Press Network under the Advanced Tab
• In the Cached Web Content section, click Clear Now (button).
• Quit Firefox and restart it
Option 2 to install the certificates (very tedious manual):
Click Firefox (word) (upper left of your screen)
Preferences
Advanced (tab on left side of screen)
Certificates (tab)
View Certificates (button)
Authorities (tab)
Import (button)
Browse to the DoD certificates (AllCerts) extracted folder you downloaded and extracted above.
Note: You have to do this step for every single certificate
Note2: If the certificate is already in Firefox, a window will pop up stating: 'Alert This certificate is already installed as a certificate authority (CA).' Click OK
Note3: If the certificate is not already in Firefox, a window will pop up stating 'You have been asked to trust a new Certificate Authority (CA).'
Check all three boxes to allow the certificate to: identify websites, identify email users, and identify software developers
Once you've added all of the certificates..
• Click Firefox (word) (upper left of your screen)
• Preferences
• Advanced (tab)
• Press Network under the Advanced Tab
• In the Cached Web Content section, click Clear Now (button).
• Quit Firefox and restart it
Step 6: Decide which CAC enabler you can / want to use
Only for Mac El Capitan (10.11.x or older)
After installing the CAC enabler, restart the computer and go to a CAC enabled website
NOTE: Mac OS Sierra (10.12.x), High Sierra (10.13.x), Mojave (10.14.x) or Catalina (10.15.x) computers no longer need a CAC Enabler.
Try to access the CAC enabled site you need to access now
Mac support provided by: Michael Danberry
